Cloudflare Turnstile helps reduce automated form abuse, but it does not stop all Elementor form spam on its own.
Modern spam bots increasingly behave like real users. They can load JavaScript, pass browser challenges, interact with forms, and even submit requests through real browsers or low-cost human-solving farms. That means many WordPress sites continue receiving Elementor spam submissions even after enabling Turnstile.
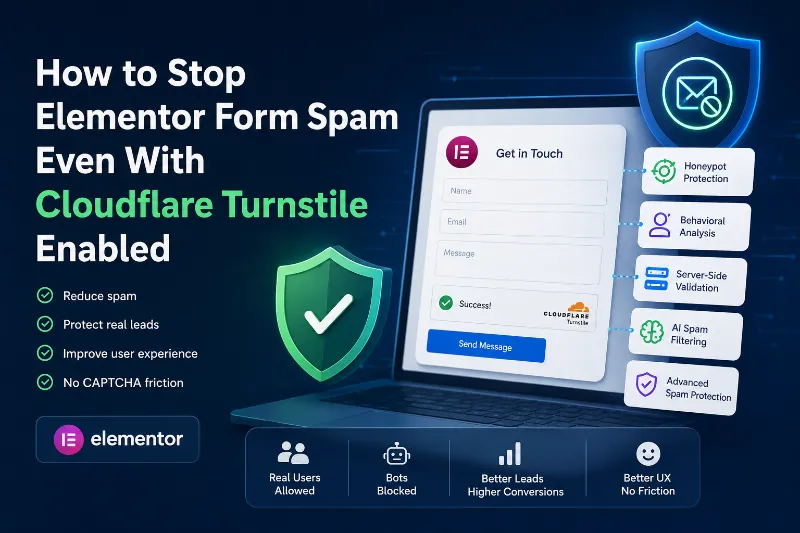
The practical solution today is layered spam protection:
- Browser-level verification (like Turnstile)
- Honeypot traps
- Behavioral analysis
- Server-side validation
- Content analysis
- AI-based spam detection
- Rate limiting and submission monitoring
This article explains why Elementor forms still receive spam, what Cloudflare Turnstile actually protects against, where it falls short, and how to build a more resilient anti-spam setup without damaging conversions.
TL;DR
| Protection Layer | Main Strength | What It Misses | User Experience | Recommended Usage |
|---|---|---|---|---|
| Google reCAPTCHA | Blocks basic automated bots | Human-solving farms, browser automation, token abuse | Often frustrating for legitimate users | Partial layer only |
| Cloudflare Turnstile | Better UX with reduced friction | Advanced browser automation and direct POST spam | Smooth and privacy-friendly | Strong frontend layer |
| Honeypot Fields | Invisible bot trapping | Adaptive or behavior-aware bots | Completely invisible to users | Recommended secondary layer |
| Rate Limiting | Reduces spam bursts and abuse | Slow distributed attacks using residential proxies | Invisible | Useful supporting layer |
| Behavioral Detection | Detects human-like spam patterns | Requires advanced analysis logic | Invisible | Highly recommended |
| AI Spam Filtering | Understands message intent and spam signals | May require tuning for edge cases | Invisible | Recommended for high-spam sites |
| Server-Side Validation | Protects against direct endpoint abuse | Needs proper backend implementation | Invisible | Essential protection layer |
| Layered Spam Defense | Combines multiple detection methods | Requires proper configuration | Strong protection with low friction | Best modern approach |
The most effective Elementor spam protection today is a layered approach where Turnstile is one layer, not the entire defense system.
Why Elementor Forms Still Receive Spam
One Elementor site we analyzed received over 1,800 spam submissions in 12 days even after enabling Turnstile.
The reason is simple:
Modern spam is no longer limited to primitive bots blindly posting HTTP requests.
Today’s spam ecosystem includes:
- Headless browsers
- AI-assisted form filling
- Browser automation tools
- Human-assisted spam farms
- Residential proxy networks
- Real browser sessions with JavaScript enabled
In practice, this means bots can now:
- Load Elementor forms normally
- Execute JavaScript
- Pass browser-based challenges
- Simulate mouse movement
- Wait realistic timing intervals
- Submit forms like legitimate visitors
This is especially common on:
- Elementor contact forms
- WooCommerce checkout forms
- Quote request forms
- Lead generation forms
- Newsletter signup forms
Sites that receive significant traffic often become targets because spam campaigns are largely automated and opportunistic.
What Cloudflare Turnstile Actually Does
Cloudflare Turnstile is designed primarily as a CAPTCHA alternative.
Instead of forcing users to solve image puzzles, Turnstile analyzes browser and network signals to determine whether a visitor appears legitimate.
This improves UX dramatically compared to traditional CAPTCHA systems.
What Turnstile Is Good At
Turnstile is very effective against:
- Simple automated scripts
- Non-browser spam bots
- Basic cURL-based attacks
- Large volumes of unsophisticated automation
- Some credential stuffing attempts
Compared to older CAPTCHA systems, it also offers:
| Feature | reCAPTCHA | Turnstile |
|---|---|---|
| Visual challenges | Frequent | Rare |
| User friction | Higher | Lower |
| Accessibility | Mixed | Better |
| Privacy concerns | Higher | Lower |
| Conversion impact | Sometimes negative | Usually lower |
For many websites, enabling Turnstile immediately reduces spam significantly.
But reduced spam is not the same as eliminated spam.
Common Ways Bots Bypass Turnstile
This is where many Elementor site owners get confused.
Turnstile is not “broken.” It simply solves a narrower problem than many people assume.
1. Real Browser Automation
Modern bots use tools like:
- Puppeteer
- Playwright
- Selenium
- Headless Chrome
These tools launch actual browsers capable of passing many browser-level checks.
The spammer essentially automates a realistic browser session.
2. Human-Assisted Spam
Some spam operations route CAPTCHA challenges to real humans.
This is surprisingly inexpensive at scale.
The result:
- Turnstile validation succeeds
- The form still receives spam
3. Low-Volume Spam Campaigns
CAPTCHA systems are strongest against high-volume automation.
But many modern spam campaigns intentionally stay low volume to avoid detection.
For example:
- 3-10 submissions per hour
- Distributed across rotating IPs
- Different message content each time
These patterns often look “human enough.”
4. Compromised Browsers and Devices
Some spam originates from infected residential devices.
From the server’s perspective:
- The browser looks legitimate
- The IP looks residential
- JavaScript executes normally
- Turnstile validation passes
5. Form Endpoint Abuse
In some WordPress configurations, attackers bypass frontend rendering entirely and submit directly to backend endpoints.
If server-side validation is weak, submissions may still succeed.
This is especially important for:
- AJAX forms
- Custom Elementor workflows
- API-connected forms
Why CAPTCHA Alone Is No Longer Enough
CAPTCHA systems were originally designed during a very different era of spam prevention.
Back then, many bots:
- Did not execute JavaScript
- Did not emulate browsers
- Used obvious automated requests
Today’s spam landscape is fundamentally different.
Modern Spam Detection Requires Context
Effective spam filtering now depends on analyzing patterns like:
- Submission timing
- Field interaction behavior
- Message structure
- Link patterns
- Language anomalies
- Hidden field interaction
- Repeated submission fingerprints
- Server-side reputation signals
CAPTCHA alone cannot evaluate all of this.
Better Protection Layers for Elementor Forms
The best Elementor spam protection combines multiple lightweight layers instead of relying on a single gatekeeper.
1. Honeypot Protection
Honeypot fields are invisible form fields normal users never interact with.
Bots often fill every available field automatically.
If the hidden field contains data:
- The submission is flagged as spam
Good honeypots are:
- Invisible
- Dynamically generated
- Difficult for bots to identify predictably
This remains one of the highest ROI anti-spam techniques because it adds zero user friction.
2. Behavioral Spam Detection
Behavioral systems analyze how the form was completed.
Examples include:
- Unrealistically fast submissions
- No mouse or keyboard interaction
- Suspicious field completion patterns
- Identical timing fingerprints
- Repeated automation signatures
This is far more effective against sophisticated bots because it evaluates behavior rather than just browser legitimacy.
3. Server-Side Validation
Client-side validation alone is never sufficient.
Strong anti-spam systems validate submissions on the server side before:
- Sending emails
- Creating orders
- Saving leads
- Triggering automations
Important server-side checks include:
- Field consistency
- Header validation
- Origin checks
- Suspicious payload detection
- Encoding anomalies
4. AI-Based Spam Filtering
AI filtering is becoming increasingly useful for Elementor spam protection.
Instead of only checking technical fingerprints, AI systems analyze:
- Message intent
- Language structure
- Semantic patterns
- Spam probability
For example, AI can often identify:
- SEO spam
- Fake lead submissions
- Generic outreach spam
- AI-generated junk messages
- Repeated commercial solicitation
This matters because modern spam increasingly resembles legitimate human writing.
5. Rate Limiting and Fingerprinting
Good spam protection also monitors:
- Submission frequency
- IP behavior
- Browser fingerprints
- Session anomalies
This helps stop:
- Burst attacks
- Distributed low-volume campaigns
- Automated retries
Real-World Elementor Spam Examples
Here are common spam patterns frequently seen in Elementor forms.
SEO Spam
Example:
“Hello dear website owner, we can improve your Google rankings…”
Characteristics:
- Generic marketing language
- Suspicious links
- Rotating domains
- Often human-assisted
Turnstile may allow these because the browser session appears legitimate.
AI-Generated Contact Spam
Example:
“I recently visited your excellent website and wanted to discuss a mutually beneficial collaboration opportunity.”
Characteristics:
- Grammatically polished
- Generic business tone
- Slightly unnatural phrasing
- Generated at scale
Traditional CAPTCHA systems struggle here because technically the submission looks human.
WooCommerce Checkout Spam
Examples include:
- Fake orders
- Card testing
- Coupon abuse
- Abandoned spam checkouts
Turnstile can reduce automation but usually needs:
- Rate limiting
- Fraud monitoring
- Behavioral analysis
How MASPIK Adds Deeper Spam Protection
Maspik is designed to work inside WordPress itself rather than acting only as a browser challenge layer.
That distinction matters.
Instead of only asking:
“Does this visitor appear human?”
MASPIK also evaluates:
“Does this submission behave like real user intent?”
Protection Layers MASPIK Adds
Behavioral Detection
MASPIK analyzes submission behavior patterns that often indicate automation.
This helps catch:
- Fast scripted submissions
- Repeated bot patterns
- Suspicious interaction behavior
Honeypot Protection
The plugin includes invisible honeypot techniques designed to trap automated submissions without affecting real users.
Server-Side Spam Validation
Validation happens directly inside WordPress before the submission proceeds further.
This is important because frontend-only checks can sometimes be bypassed.
AI Spam Filtering
MASPIK also supports AI-assisted spam analysis for detecting:
- AI-generated spam
- SEO outreach spam
- Generic solicitation
- Contextually suspicious submissions
WordPress Form Ecosystem Support
MASPIK supports major form builders including:
- Elementor Forms
- Contact Form 7
- WPForms
- Fluent Forms
- Gravity Forms
- WooCommerce
This is useful for agencies managing multiple client stacks.
Recommended Elementor Anti-Spam Setup
For most Elementor websites, this layered setup works extremely well:
| Layer | Recommended Tool |
|---|---|
| Browser challenge | Cloudflare Turnstile |
| Honeypot | MASPIK or native honeypot |
| Behavioral analysis | MASPIK |
| Server-side validation | MASPIK |
| AI spam filtering | MASPIK AI layer |
| Rate limiting | Cloudflare or server-level |
| Email/domain filtering | Optional additional layer |
This combination keeps friction extremely low while dramatically improving detection quality.
Practical Implementation Advice
If You Already Use Turnstile
Do not remove it.
Turnstile is still valuable because it:
- Reduces basic automated traffic
- Improves UX compared to CAPTCHA
- Blocks many low-quality bots early
The goal is not replacing Turnstile.
The goal is complementing it.
Avoid Overusing CAPTCHA Challenges
Aggressive CAPTCHA settings often:
- Reduce conversions
- Hurt accessibility
- Frustrate mobile users
- Increase abandonment rates
This is especially harmful for:
- Lead generation sites
- WooCommerce stores
- Service businesses
- Mobile-heavy traffic
Invisible layered detection usually performs better long term.
Monitor Spam Patterns
Do not only count spam volume.
Look for:
- Similar wording patterns
- Submission timing
- Country distribution
- Repeated links/domains
- Field-specific abuse
These patterns reveal which protection layers are missing.
FAQ
Does Cloudflare Turnstile stop all Elementor spam?
No.
Turnstile reduces many forms of automated abuse, but advanced spam can still pass through legitimate browser sessions or human-assisted workflows.
Why am I still getting spam after enabling Turnstile?
Usually because:
- The spam uses real browsers
- The spam is human-assisted
- The attack volume is intentionally low
- The form lacks deeper server-side analysis
Is Turnstile better than reCAPTCHA for Elementor?
For UX, usually yes.
Turnstile generally creates less friction and fewer visual challenges while still blocking many basic bots.
What is the best CAPTCHA alternative for Elementor?
The best modern approach is not replacing CAPTCHA with another single tool.
It is combining:
- Turnstile
- Behavioral analysis
- Honeypots
- Server-side validation
- AI filtering
Can honeypots stop Elementor spam?
They help significantly against many automated bots and add zero friction for users.
However, advanced bots may detect simple honeypots, which is why layered protection is recommended.
Does AI spam filtering help with Elementor forms?
Yes.
AI filtering is increasingly effective against:
- AI-generated spam
- SEO outreach spam
- Human-written solicitation spam
- Contextually suspicious submissions
Especially when combined with behavioral analysis.
Final Thoughts
Elementor form spam is no longer just a CAPTCHA problem.
Modern bots increasingly behave like real users, which means browser verification alone cannot reliably distinguish legitimate submissions from sophisticated spam.
Cloudflare Turnstile remains an excellent first layer because it improves user experience while blocking large amounts of low-quality automation.
But for websites that rely heavily on leads, orders, bookings, or customer inquiries, deeper server-side protection is now essential.
The most reliable approach today is layered:
- Turnstile for browser-level filtering
- Honeypots for silent bot trapping
- Behavioral analysis for automation detection
- AI filtering for content evaluation
- Server-side validation for final verification
That combination protects forms more effectively without turning legitimate visitors into CAPTCHA testers.

